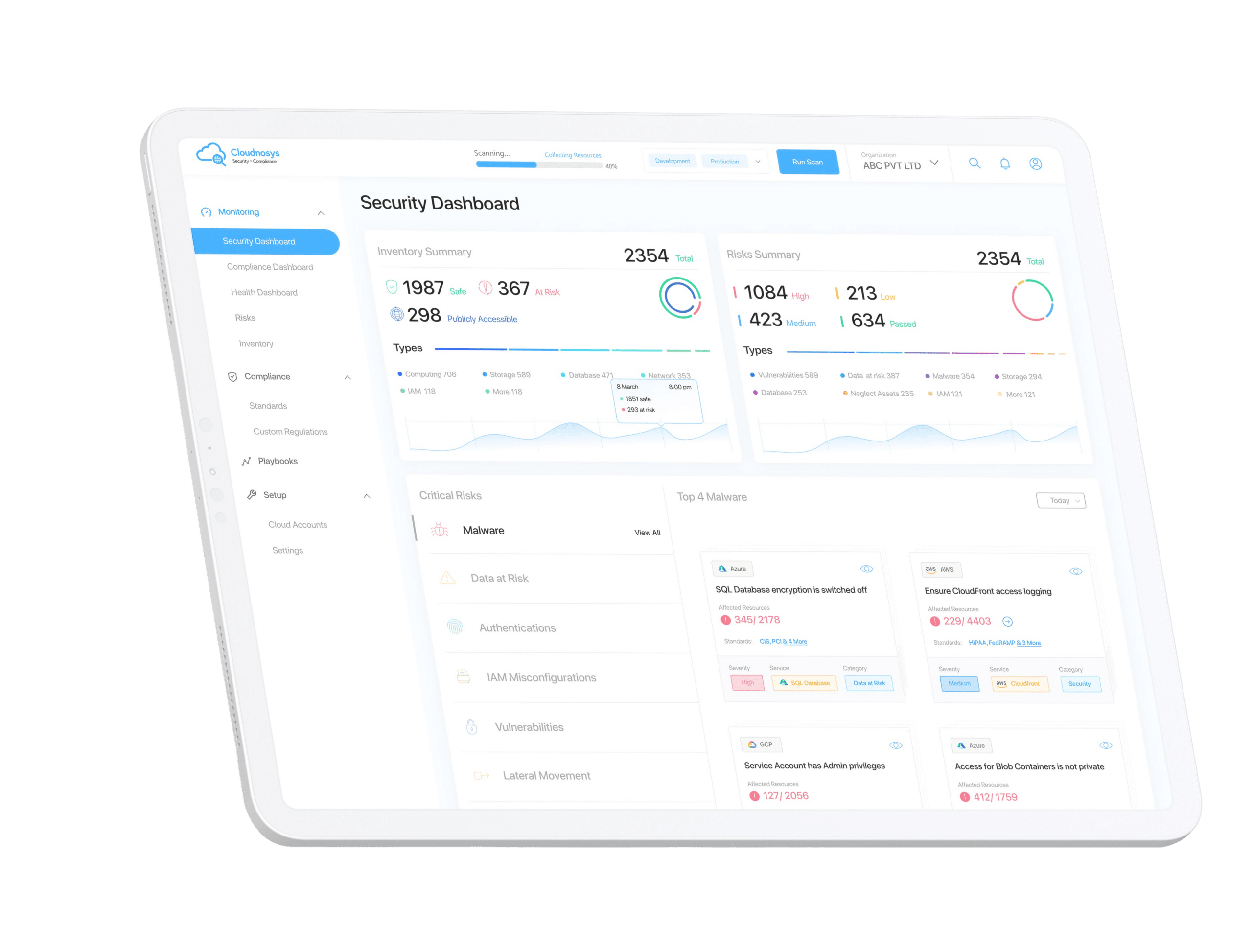
Full Stack Cloud Security Platform
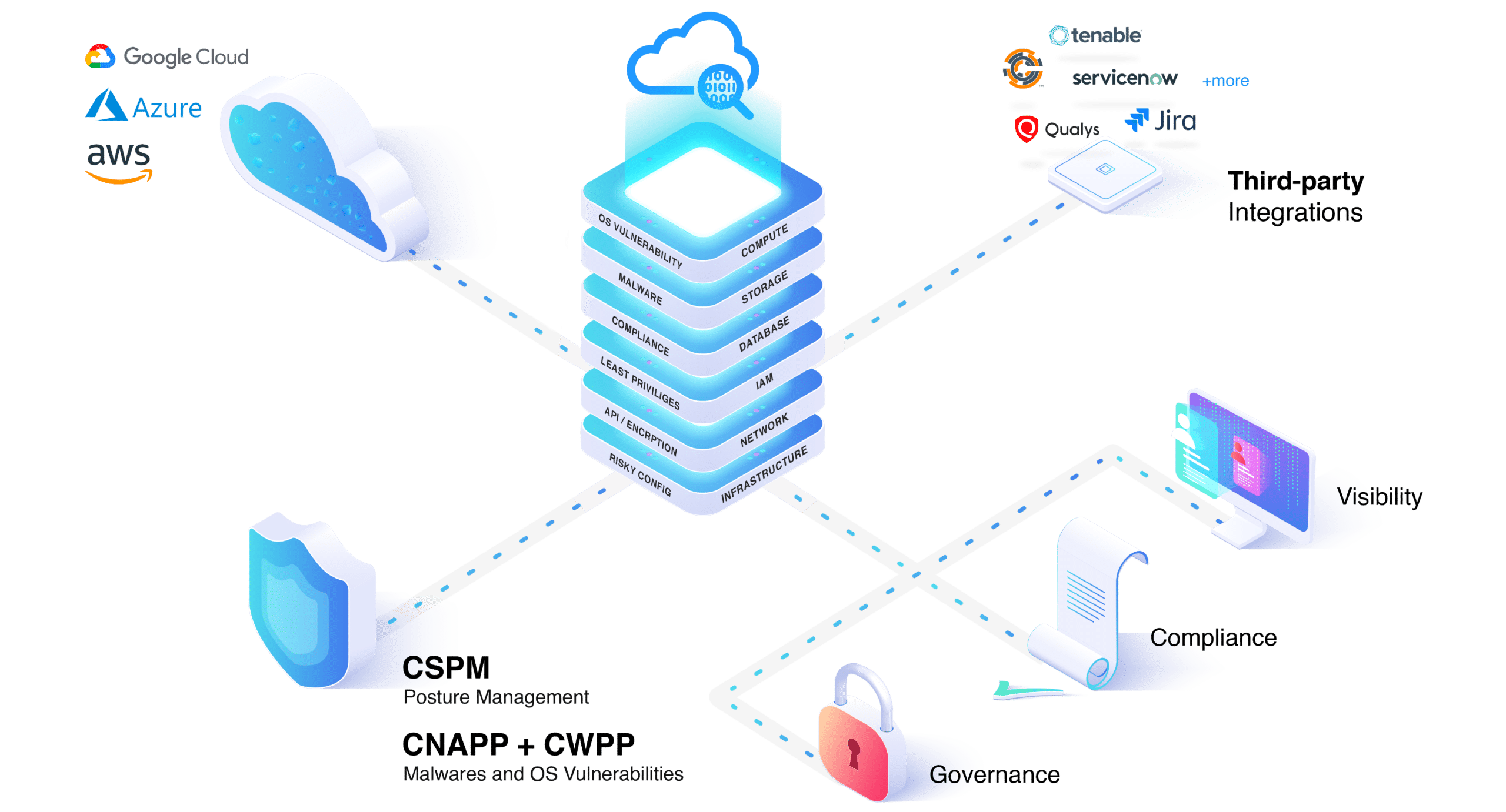
Full stack coverage with risk prioritization, compliance, SOAR remediations, misconfigurations, OS vulnerabilities, malware, context-aware alerts, and third-party integrations.

Five Tools In One!
Full Stack Cloud Security and Compliance for Public Clouds
Vulnerability (CVE), Malware, Posture Management,
SOAR, Compliance.
Setup in under
10 mins
Agentless SaaS or Hosted
Alert Fatigue
91% less
Prioritize top 1% of Alerts
Remediate in under
2 mins
Policy Driven Remediations
What Customers Are Saying

“We were challenged with PCI compliance for the cloud. CloudEye centralize compliance policy management and enforcement for all of our cloud services to meet PCI”
– George Carr
Senior Network Security Architect

“We deployed Cloudnosys in minutes and were amazed at the visibility and control we gained over our entire global cloud footprint for compliance and security. The platform helped us maintain our cloud infrastructure compliance posture and kept regulators satisfied during audits“
– Mark Schlake
Director of Product Strategy, Security, and Risk
“We needed to secure our multi-cloud approach and protect our healthcare patient data. We wanted a solution that was automated and guided us step by step with remediations after finding and meet our HIPPA, GDPR compliance needs. Cloudnosys helped us achieve all of these and more including reporting for the board in record time and minimal costs.”
– André Barros
Director of Security and Compliance
Explore Our Platform
Agentless Scanning
Scans cloud infrastructure and applications without requiring an agent installation, reducing complexity and overhead while improving security with continuous scanning capabilities.
Malware Analysis
Analyzes malicious software to identify its behavior and potential impact on the system, enabling the detection and remediation of malware attacks in cloud infrastructure and applications.
Vulnerability Management
Identifies, prioritizes, and remediates vulnerabilities in cloud infrastructure and applications through a process that includes risk prioritization, risk assessment, and remediation planning and execution.

Attack Path Analysis
Enables proactive detection and remediation of potential security risks by identifying potential attack paths that cyber attackers may use to access critical assets.
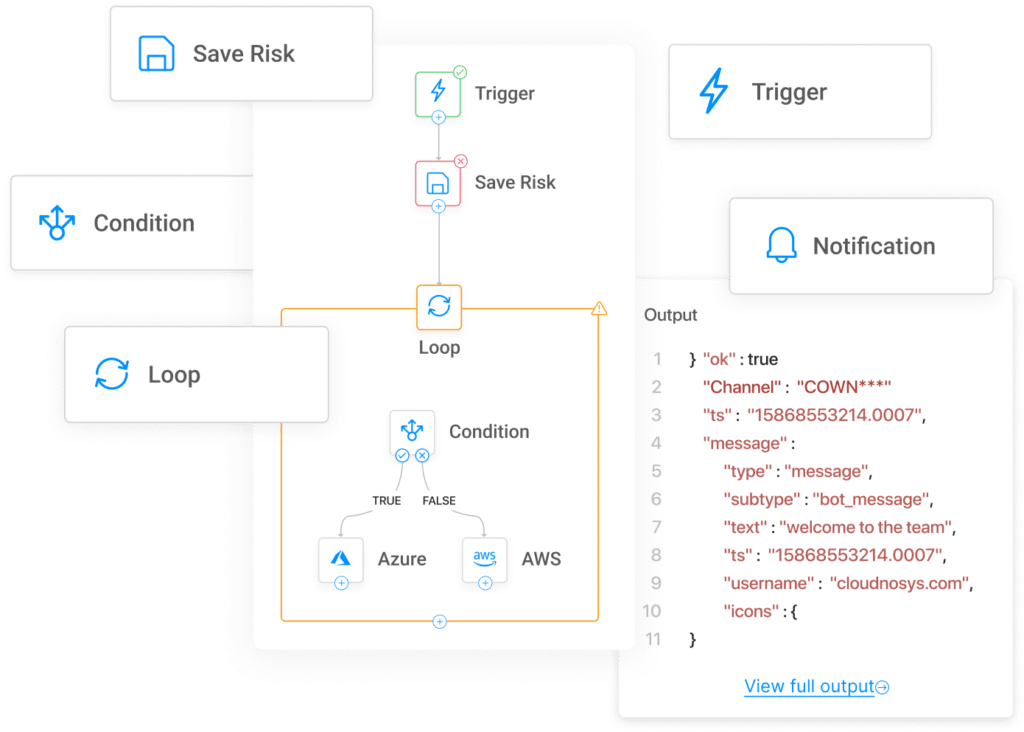
SOAR
SOAR can automate and orchestrate cloud security incident response, eliminating the need for custom coding and swivel chair analysis in multiple tools. This can help organizations improve their security posture and reduce the risk of data breaches.
Real Time Threat Detection
Real time threat detection feature uses machine learning to identify and respond to threats in real time. This helps to protect your cloud environment from a wide range of attacks.
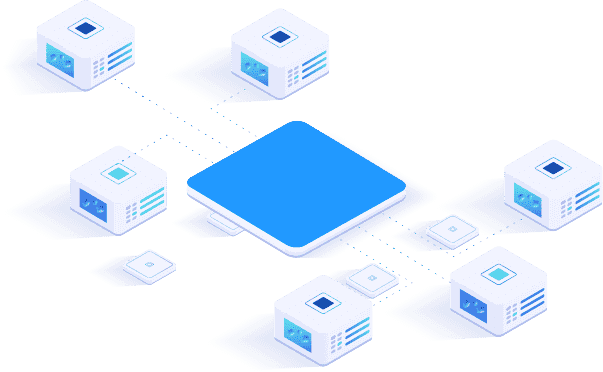
CNAPP
Cloud Native Application Protection Platform (CNAPP) offers comprehensive security features for cloud applications, including vulnerability management, agentless scanning, and malware analysis. Our CNAPP delivers multiple tools and capabilities into a single solution to reduce complexity and delivers risk prioritization using native graph analysis. From development to production in one solution.

CWPP
Cloud Workload Protection Platform (CWPP) offers a range of security native features for cloud workloads, including malware analysis, vulnerability management for files and OS, and agentless scanning that reduces operational overhead and architecture changes.
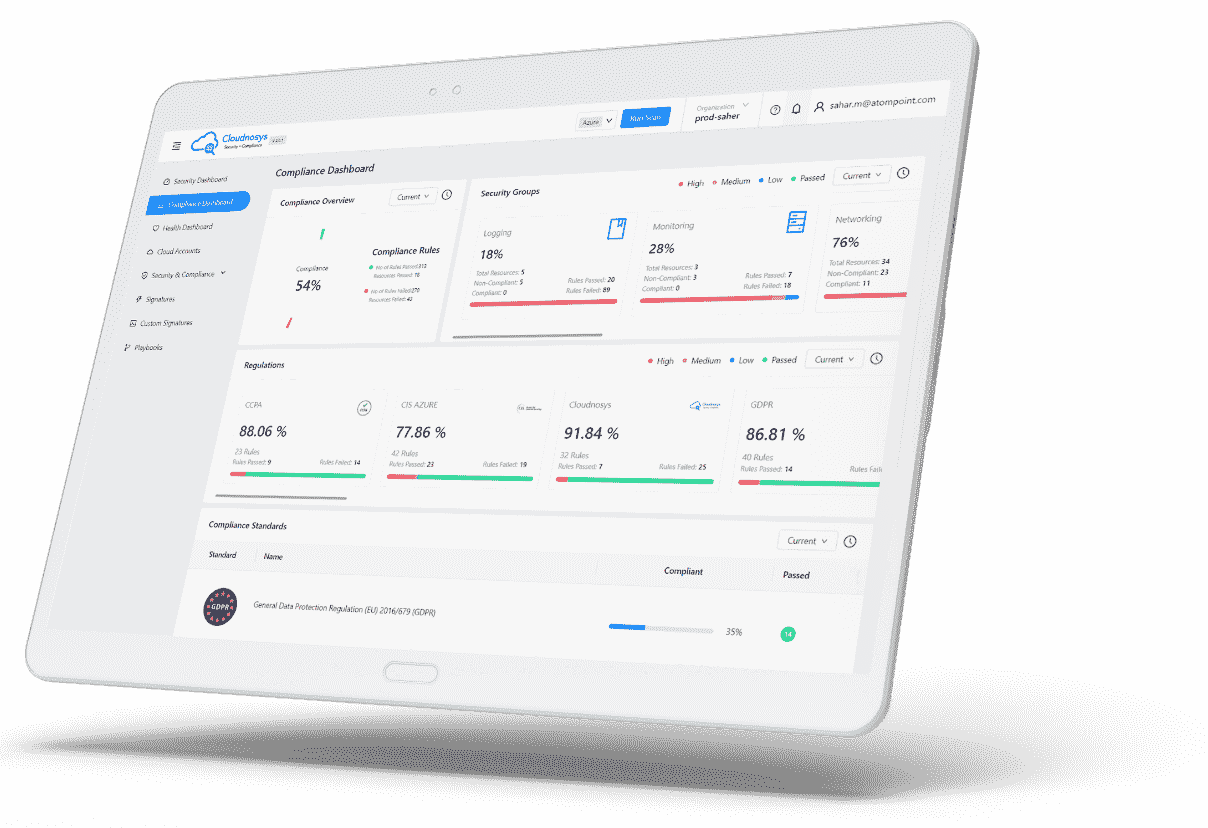
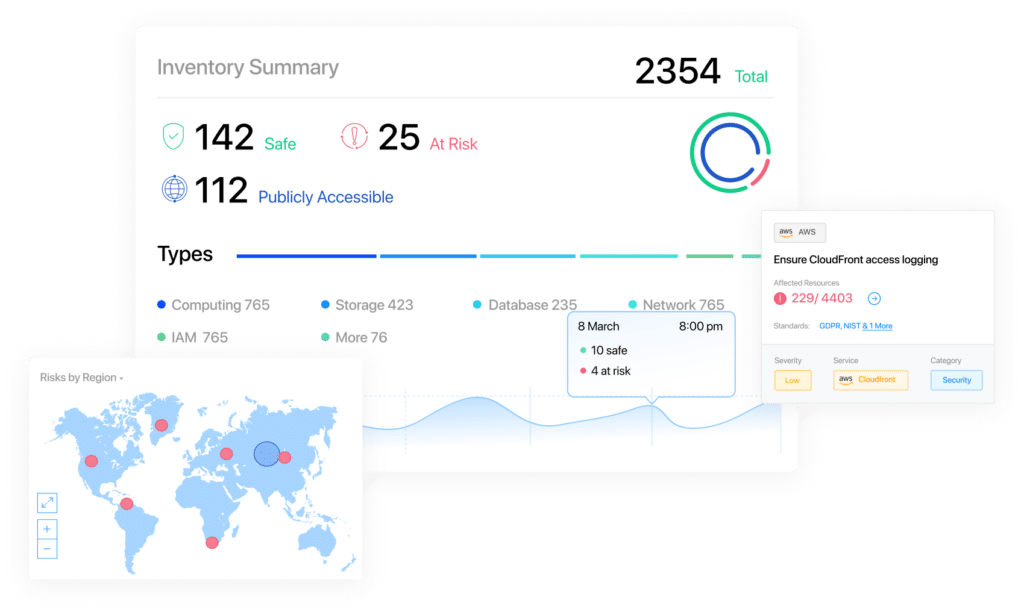
CSPM
Enables automated security checks, visibility into cloud environments, compliance streamlining, and improved overall security posture. Continuously monitors cloud infrastructure and applications, identifies and remediates potential security risks, and tracks compliance in real-time, ensuring secure and compliant cloud infrastructure..
What We Offer
Visibility
See and secure your cloud with actionable context, gain visibility and control of all your security threats, vulnerabilities, configurations, risks, policies, and user activities. Prevent data loss, configuration drift, and unauthorized access.
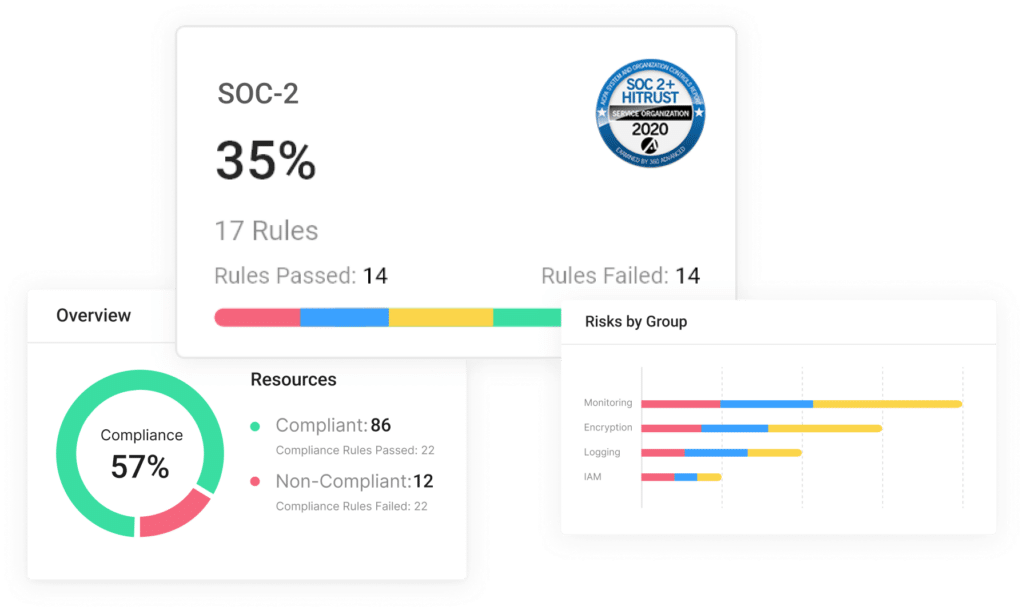
Compliance
Monitor and speed up compliance assessment, audit management, and reporting. Leverage our extensive set of regulations including HIPAA, PCI, GDPR, ISO27001, NIST, CIS, and more

Governance
Automate your cloud with confidence by enforcing standard and custom policies across users, accounts, projects, regions, and virtual networks. Enforce drift control and auto remediate to reduce alert fatigue.
Why Do You Need In Dynamic Cloud Security?

Your Challenge
YOUR GOAL
Your Challenge
YOUR GOAL

Your Challenge
YOUR GOAL
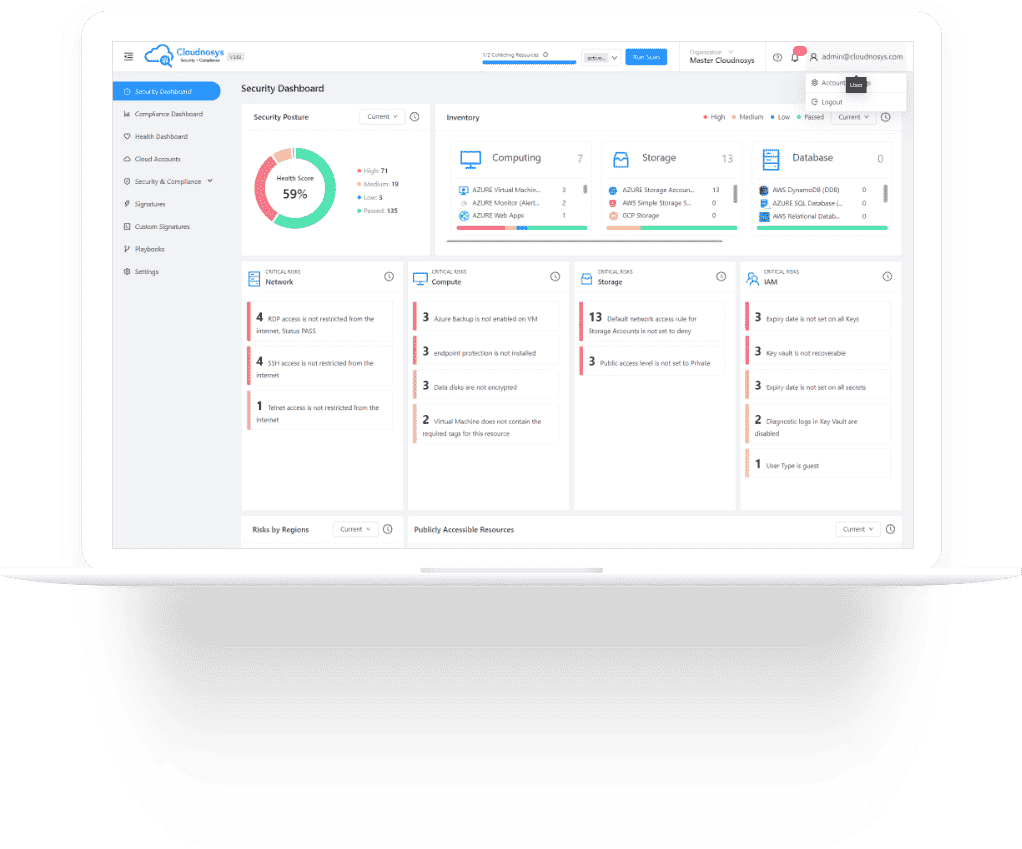
Full Context Security
A unified picture of all threats based on machine data and contextual analysis that provides cloud security and compliance. Cloudnosys dynamically remediates and heals your cloud using best practice standards to ensure compliance with little effort. The future of full stack, context-aware cloud security is here – and it starts with Cloudnosys.
Featured Blogs

Vulnerability Remediation: Strengthening Your Digital Defenses
In today’s interconnected world, the digital landscape is rife with potential vulnerabilities that cyber attackers can exploit. “Vulnerability remediation” is a crucial aspect of cybersecurity,

Auto Remediation: Enhancing Efficiency and Security in the Digital Landscape
In the fast-paced world of technology, ensuring the smooth functioning and security of digital systems is of paramount importance. “Auto remediation” is a term gaining
Cloud Security Frameworks: Unlocking the Key to Secure and Resilient Cloud Environments
In today’s digital landscape, where businesses heavily rely on cloud computing, ensuring the security and compliance of cloud environments has become a top priority. Cloud
Frequently Asked Questions
Cloudnosys is a cloud security platform that protects cloud infrastructures from security threats, vulnerabilities, and compliance risks.
It provides visibility and continuous monitoring over cloud security, and compliance in AWS, Azure, and GCP. It runs complete scans on your cloud infrastructure over pre-written and custom signatures (protocols) and then generates a report of the loopholes present and detected.
Our customizable JSON scripts based playbooks help you to remediate and integrate threats and vulnerabilities.
These easy to create playbooks, with automated trigger types, scan and remediate the errors in the relevant cloud account.
Cloudnosys empowers its clients to solve cloud infrastructure security issues. It identifies and provides a step-by-step guide to rectify security vulnerabilities, performance errors, cost inefficiencies, and reliability risks.
Cloudnosys supports the 3 public cloud leaders:
- Amazon Web Services
- Google Cloud Platform
- Microsoft Azure
Compliance with cloud infrastructure is a key area of the Cloudnosys platform.
We support all major compliance standards like PCI, ISO 27001, HIPAA, SOC 2, GDPR, etc.